Proactive vs. Reactive Cybersecurity
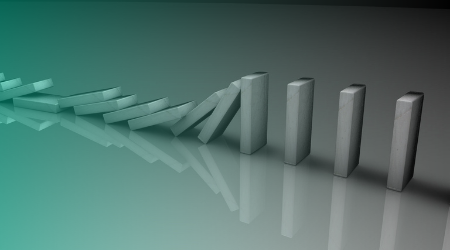
Many businesses already spend a great deal on cybersecurity but are still inadequately prepared, and the solution often lies in their general approach. Reactive and proactive cybersecurity follow different approaches and offer unique benefits, and these two approaches also require different processes and tools to maximize cybersecurity.
Which of these security approaches is more effective for your business? Is either of them already more dominant in your organization? Understanding how the adoption of these strategies will affect your cybersecurity posture is crucial to improving your defenses.
What is Reactive Security
Reactive cybersecurity involves implementing mechanisms designed to defend a business against cyberattacks and respond to malicious characters that have already compromised your network security, very similar to how our bodies deal with illnesses. Imagine a biological virus or any common bug like the flu, our body only responds to these issues as they enter our bodies, they are 100% reactive. Once the bug enters our system, our body identifies it, sometimes for the first time, and then works on mitigating the threat. Reactive security typically consists of tools like antivirus software, firewalls, password managers, spam filters, and ad-blockers. The reactive approach to security generally aims to cover the following.
- Network monitoring for anomalies.
- Forensics and incident response, especially after a breach.
- Anti-spam and anti-malware protection.
- Firewall protection.
Although firewall protection is reactive, it is sometimes considered proactive because of its ability to block unwanted traffic. It is essential to understand that while reactive cybersecurity is excellent for preventing cyber attackers from causing excessive havoc, it can become a problem when businesses rely on a reactive approach as their sole defense mechanism. This introduces the need for proactive security strategies.
What is Proactive Security
Proactive cybersecurity takes an entirely different approach from reactive. It works towards preventing a cyberattack or breach from occurring in the first place, in the same way as a vaccine would preventing you from catching the flu. When flu season is around the corner, health organizations recommend getting a flu shot to prevent us from getting sick and catching it in the first place. Adopting proactive cybersecurity strategies will help you to identify any existing vulnerabilities in your network or system before malicious entities can exploit them.
Proactive strategies involve penetration testing, network monitoring, security audits, employee training, and threat intelligence gathering. Some proactive cybersecurity tools include:
- Threat Hunting Solutions.
- Privileged Access Management systems
- Cyber Threat Intelligence tools.
- Security awareness training platforms.
- Pentesting tools.
- Intrusion Prevention Systems.
However, in the event of a data breach or cyberattack, your top priority would be to provide a robust response, and that’s what reactive cybersecurity does.
Going Beyond Reactive in The Current Cybersecurity Landscape
A while ago, having simple cybersecurity solutions like antivirus and a firewall was sufficient for most companies to work with. However, the current state of cybersecurity has dramatically evolved and intensified since then. For example, from 2009 to 2018 there was a 440% increase in global cyberwarfare attacks, this is even before the COVID-19 outbreak that skyrocketed cyber-attacks to a whole new level. Hacker sophistication is also rapidly rising, and businesses must be more creative than ever in defending their priced assets. For small businesses with minimal cybersecurity budgets, adopting a reactive approach is usually the easiest choice. Outsourcing cybersecurity services can help many SMBs avert this concern and become more proactive.
With experts predicting cybercrime costs to reach $6 billion this year (2021) and surpass $10 billion by 2025, businesses must do more than react. In addition to their current reactive strategies, business leaders must invest in implementing proactive strategies that help their organizations identify vulnerabilities and threats before malicious entities do. Additionally, the current cybersecurity climate mandates the need for enterprises to monitor their environments consistently and observe cybersecurity trends across their industries.
Drawbacks of Reactive Cybersecurity
Constantly putting out fires
Rather than following a planned, strategic format, a reactive approach to cybersecurity puts your business in a position where you’re constantly responding to new threats as they arise. Considering that the average cost of data breaches in the U.S. is $8.6 million, this can be a costly gamble to take.
You’re always one step behind
As of 2020, the World Economic Forum reported that the cyberattack detection rate is as low as 0.05% across the United States. The truth is that most businesses will miss the early signs of cyberattacks until the malicious entities have already started causing havoc.
Regulation and compliance standards are rising
With the largest GDPR fine thus far standing at €746,000,000, regulation and compliance standards are rising, and they require some businesses to take proactive steps in protecting users’ data. For instance, compliance with the General Data Protection Regulation (GDPR) requires companies to take a series of proactive steps in ensuring and maintaining data security.
You are always in danger
Cybercriminals are constantly renewing their tactics to become more sophisticated. If you adopt reactive strategies, you’ll frequently have to relearn how to respond to these dynamic threats. If you adopt reactive security strategies exclusively, you’ll need to be prepared to deal with a higher level of danger at all times.
The Benefits of Proactive Cybersecurity
Without a proactive cybersecurity approach, your business is constantly at risk of a data breach. However, the adoption of proactive security strategies will allow you to take preemptive steps against cybercriminals.
It costs less to clean
They say prevention is better than cure. This is precisely the case with responding to cyber threats, and it costs significantly less in time and resources to proactively secure and patch vulnerabilities before malicious actors strike. Would you rather pay upfront to prevent a data breach, or pay afterward to clean up? Without proactive cybersecurity, businesses can expect outrageous clean-up costs like fines, settlement, and loss of business in the event of a breach. For instance, Target’s data breach back in 2013 amounting up to $18,500,000.
Seamlessly uncover insider threats
Reactive cybersecurity strategies only address external threats facing your organization. However, proactive cybersecurity strategies can help you look inwards and catch or stop insider threats. Research shows that insider threats are responsible for 22% of data breaches globally, which makes adopting proactive security strategies even more crucial.
Constantly strengthen and mature your cyber posture
In response to today’s cybersecurity challenges, it’s become more important than ever to have a clear vision of your cybersecurity environment. Adopting a proactive approach helps you understand your security landscape and make the relevant optimizations to suit your business needs.
Closing Thoughts
For decades, enterprises have mostly adopted a reactive approach to combating cybersecurity threats. While this is great, it’s only one part of the puzzle. As cyber threats are becoming more complex and sophisticated, businesses must adopt a well-rounded approach to mitigating these risks. Combining reactive and proactive cybersecurity approaches completes the puzzle.
CYREBRO helps you stay ahead of threats and constantly strengthens your cyber posture with a Single Cyber Brain. Driven by Threat Intelligence and Threat Hunting, CYREBRO provides proactive cyber security that integrates organizations’ existing security tools, leveraging them to their full potential.

