-

Choosing the Right Security Operations Model: SOC vs. SOCaaS vs. MDR
Cultivating a resilient security posture is much like tending a garden—it requires continuous care, evolving strategies, and growing expertise. Every organization’s “garden,” or attack surface, is different. Some span multi-cloud environments and global offices; others are smaller but equally critical. Just as gardens vary in size and complexity, so do the approaches to cybersecurity. An…
-

AI-Based SOCs: Smarter, Faster, and More Secure (Part 2)
In the 2nd part to our previous post, which reviewed the limitations of traditional Security Operations Centers (SOCs), the rise of AI-powered SOCs, and their key components, we’ll cover the practical impact of AI-driven SOCs and Managed Detection and Response (MDR) solutions. By integrating multiple AI and machine learning (ML) models, these forward-thinking solutions bolster…
-

AI-Based SOCs: Smarter, Faster, and More Secure (Part 1)
Steam engines, electricity, airplanes, the Internet – what do these things have in common? Each invention was born out of a necessity to address some of humanity’s most tedious activities and pressing challenges. This cycle of creation has never stopped, and each time society faces an unprecedented problem, innovators rise to the occasion and develop…
-
Lateral Movement: The Silent Threat and How to Combat It Effectively
In December 2020, one headline dominated cybersecurity news: SolarWinds had been the target of a massive cyberattack. The story began over a year earlier (September 2019) when state-sponsored Russian hackers gained unauthorized access to SolarWinds’ network and inserted malicious code into SolarWinds’ Orion software. In February 2020, SolarWinds released the infected software as an update,…
-

The Operational Advantages of MDR with Security Data Lakes
Learn why organizations are choosing MDR solutions with built-in Security Data Lakes to streamline incident response and reduce cybersecurity costs.
-
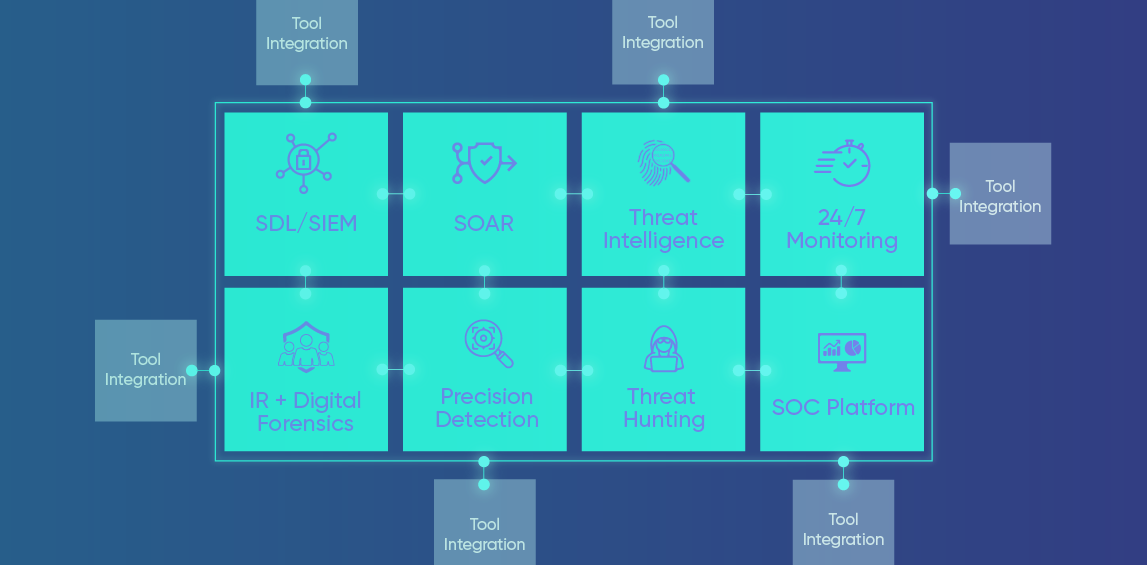
The Evolution of SecOps: The Essential Components of MDR
As threat actors launch more sophisticated and AI-enhanced attacks, traditional preventative measures alone are falling short. Adequately protecting an intricate web of modern infrastructure — a blend of on-premise and cloud-based systems, numerous mobile devices, and many applications — while navigating increasingly stringent compliance regulations demands a more proactive and holistic approach. Plenty of cybersecurity…
Loading