The Cybersecurity Arms Race – Why MDR is Your Secret Weapon

A digital arms race is afoot; how to come out on top is the question every CISO asks themselves. As the battle rages, two formidable opponents fight it out daily. On one side sit threat actors, including prolific nation-state groups from China, Russia, North Korea, and Iran. These malicious actors are well-resourced, enabling them to frequently develop new advanced persistent threats (APT) and intensify the power and capabilities of their attack weapons to achieve their given mandates – conduct government or corporate espionage, exfiltrate or corrupt sensitive data, disrupt critical infrastructure or IT networks, or influence public discourse. While the industries they target most include education (16%), government (12%), think tanks and NGOs (11%), IT (11%), and communications (6%), no sector is safe.
Cybersecurity solution developers and service providers are on the other side of the fight, constantly dissecting attack patterns and deploying defenses to counter evolving threats. In this modern-day arms race, the winner won’t only be determined by who has the biggest arsenal but also by which side can innovate faster and adapt better.
Businesses struggling to stay ahead of the curve are caught in the middle of this escalating conflict. Their challenges revolve around understanding the newest threats, keeping pace with an enemy whose weapons mutate at breakneck speeds, and investing in the right security measures to protect their valuable assets. However, their burden is compounded by the sheer volume of cyberattacks organizations face.
A Trickle-down Threat Puts Every Business at Risk
While nation-state actors might have specific geopolitical targets, the fallout from their activities impacts a much broader range of organizations. The very tools and techniques they develop often find their way onto the dark web, readily available for purchase by groups operating under the RaaS (Ransomware-as-a-Service) model and other cyber criminals. Undoubtedly, a portion of this year’s attacks – a staggering 9,478 publicly disclosed incidents as of May 2024 – were launched using purchased nation-state attack vectors.
This presents a significant challenge for businesses of all sizes, but especially SMBs, which have to grapple with additional key challenges such as:
Resource Constraints: Finding and retaining qualified cybersecurity professionals is a challenge for all organizations but nearly impossible for those with limited budgets. Without the dedicated staff to continuously monitor their networks, identify and investigate threats, and implement remediation steps, organizations can’t defend themselves properly.
Expanding Attack Surfaces: Interconnected networks, the shift towards cloud deployments, and the growing number of endpoints and mobile devices create an ever-growing attack surface with more vulnerabilities, security risks, and visibility gaps, making assets harder to monitor and secure.
Alert Overload: The volume of security alerts, most of which are false positives, can be overwhelming and lead to alert fatigue. Without proper prioritization, time and resources are wasted investigating low-risk alerts, while genuine threats could be overlooked, increasing the risk of a successful attack.
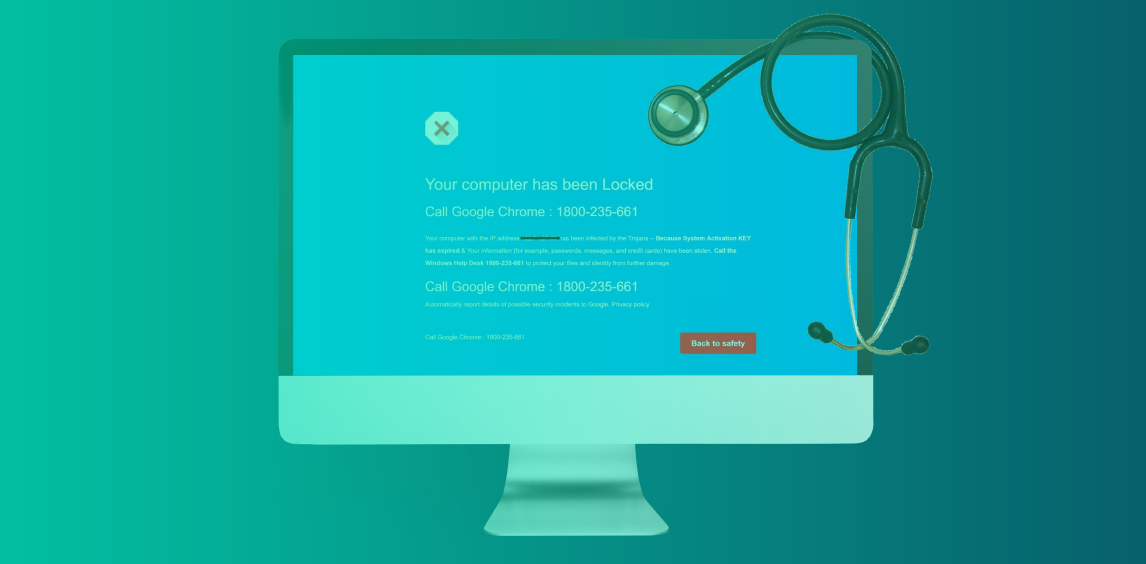
The Human Factor: Humans are fallible and can easily fall victim to the constant barrage of increasingly realistic AI-generated phishing attacks. Accidental misconfigurations, non-adherence to security protocols, and insider threats all create additional security risks.
However, challenges must be faced head-on; ignoring them only guarantees an organization’s place in the next round of statistics.
MDR: A Weapon for Modern Cyber Warriors
To have a fighting chance, businesses must adopt a new kind of weapon – one that takes a proactive and responsive approach to security. Managed detection and response (MDR) solutions do exactly that, using a combination of advanced security technologies like machine learning (ML) and Artificial Intelligence (AI) alongside expert human analysts to anticipate, contain, and mitigate risks before they materialize.
What an MDR Solution Provides
MDR services encompass several key functionalities that collectively bolster an organization’s cybersecurity posture:
Continuous Monitoring: Provides round-the-clock vigilance, swiftly identifying any suspicious behavior across an organization’s networks, endpoints, and cloud environments.
Advanced Analytics: Sophisticated tools and algorithms to analyze large volumes of data, uncover hidden threat patterns and anomalies, and enable early detection of otherwise unnoticed threats.
Expert Threat Analysis: Security analysts leverage their deep understanding of security systems and threats to prioritize and investigate alerts, ensuring efficient resource allocation.
Incident Response: Initiates an immediate response plan to confirmed breaches by isolating systems, mitigating damage, and implementing corrective measures to prevent future occurrences.
Threat Intelligence Sharing: MDR providers research and collaborate to stay updated on cyber threats, sharing this intelligence with clients to enhance their defensive capabilities.
The Benefits of an MDR
Integrating an MDR into an organization’s cybersecurity strategy offers numerous advantages:
Reduced Workload: By taking over the day-to-day responsibilities of cybersecurity, including monitoring, threat detection, and incident response, in-house IT teams can focus on strategic initiatives, improving overall organizational efficiency.
Advanced Precision Detection: MDRs can leverage advanced analytics and ML algorithms for unparalleled accuracy in threat detection. That reduces the time spent investigating false positives and the likelihood of missing critical threats while enabling proactive threat hunting based on predictive analytics.
Improved Response Times: Having a dedicated team that continuously monitors digital environments and is ready to respond, MDRs can significantly reduce the time it takes to contain a threat, minimizing potential damage.
Enhanced Compliance: MDR solutions can assist organizations in meeting various industry and regulatory compliance requirements by providing a robust security posture and detailed audit trails.
Offloading Security Monitoring: With MDR, organizations can offload the entire time-consuming responsibility of security monitoring to external experts, allowing businesses to concentrate on their core operations without the constant worry of breaches.
Enhanced Security Posture: The proactive approach of an MDR not only identifies and mitigates threats in real-time but also optimizes security configurations and eliminates vulnerabilities, ensuring organizations are always prepared and continuously boost their resilience.
The Weapon of Choice
AI and ML will be the most crucial technologies in the arms race—threat actors will build them into their weapons to devise new attacks, while security solutions developers and service providers infuse them into their defense tools.
When both sides weaponize the same technology, history shows that the outcomes are either mutual destruction or a stalemate. In cybersecurity, neither of those is acceptable; threat actors, especially state-sponsored ones, will not be deterred, and defenders, whether solution providers, service providers, or organizations themselves, will not give in.
The future looks poised to be an ongoing game of tug-of-war. On the days when the attackers pull with all their might, a comprehensive MDR is the weapon you want anchoring your side of the rope, digging in with all its capabilities to ensure your business doesn’t slide into the muddy pit of a cyberattack.